Discover EmbroideryShristi
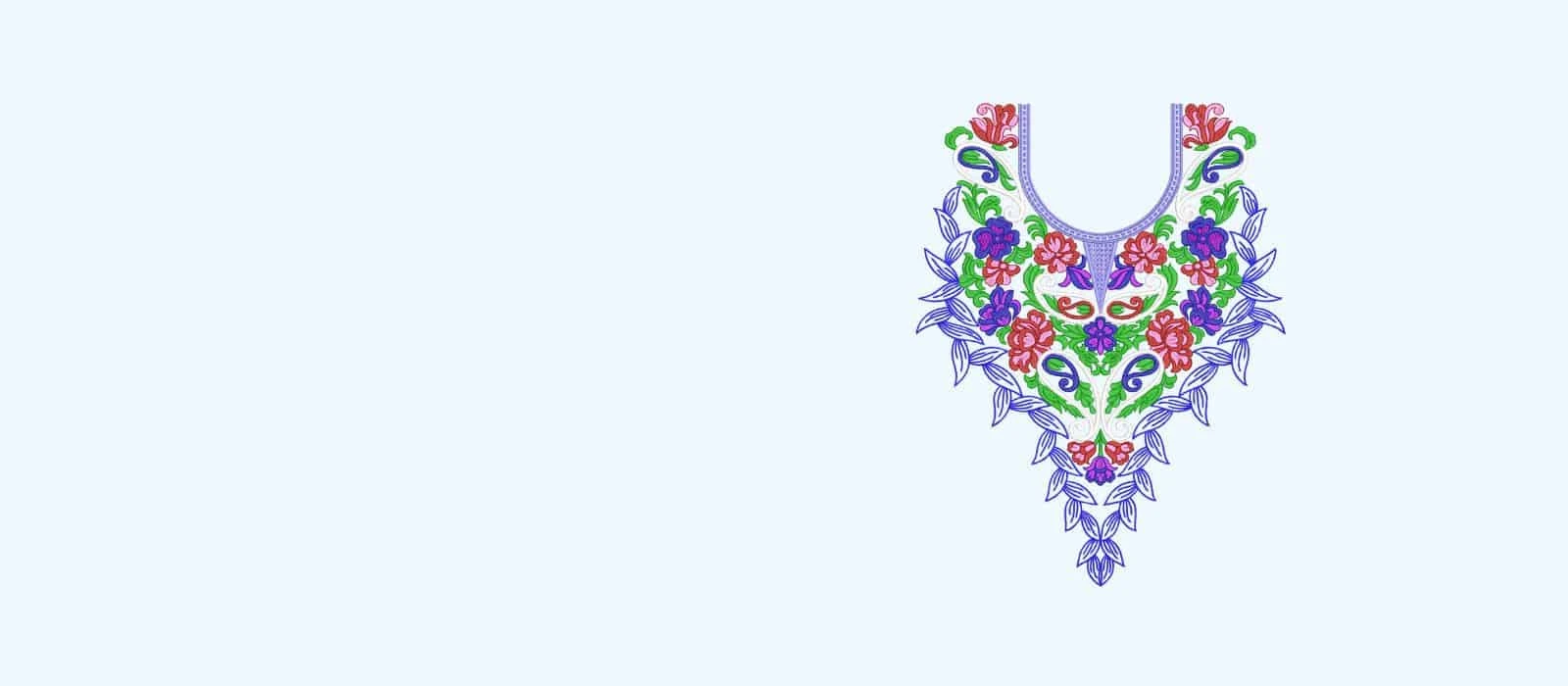
Discover a world of possibilities with our unique Embroidery Designs.
A dedicated online store for small and large hoops machine embroidery designs.
Experience the power of native EMB format:
- Easily Resize for Your Projects
- Freedom to Modify and Create
- Effortlessly Split Designs
New products

Embroidery Designs
Download Embroidery Designs from here.
Request Us
Request us for new features or embroidery designs here.
Custom Embroidery Designs
Request custom embroidery designs for the lowest price here.
$1 Dollar Store
Buy Embroidery Designs for $1 here.
Online Community
Meet other embroidery lover people here at our forum.
Video Tutorial
Check out our video tutorials at our Youtube Channel here.